by Peter Rodriguez
The following cmdlet lists current firewalls configured on your system:
|
Get-netfirewallrule | ft name, displaygroup, action, direction -wrap |
The output below shows the rule’s Name, DisplayGroup, Action and Direction. Keep in mind that this example represents an abbreviated list.

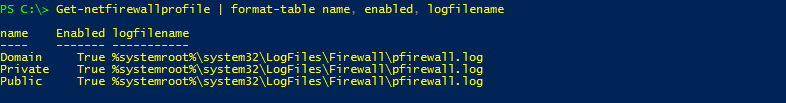
Where the Firewall Logs are located
There should be a log for each firewall profile, i.e. Public, Private and Domain, which you can find using the following cmdlet:
|
Get-netfirewallprofile | format-table name, enabled, logfilename |
Display Specific Firewall Rule Settings
Use the following cmdlet to view the features of a specific firewall rule:
|
Get-NetFirewallRule –displayname “NSClient++ Monitoring Agent” |

Enabling a Firewall Rule
To enable a firewall rule, we need to combine two cmdlets via a pipeline. For example:
|
Get-NetFirewallRule -displayname “NSClient++ Monitoring Agent” | enable-netfirewallrule |
Disable a Firewall Rule
To disable a firewall rule we [again] need to combine two cmdlets via a pipeline. For example:
|
Get-NetFirewallRule - displayname “NSClient++ Monitoring Agent” | disable-netfirewallrule |
How to List Remote IP Addresses Associated with Firewall Rule
Now, for a little advanced stuff. Let’s say that you need to know what the scope of Remote IP addresses are for a given Firewall Rule:
|
Get-NetFirewallRule -displayname “Blocking Remote IP from Threat Analysis Report” | Get-NetFirewallAddressFilter | select -ExpandProperty RemoteAddress | select -First 5 |

Final Thought
This is just scratching the surface of what you can do with Firewall Rules, using PowerShell. The following provides a list of all cmdlets associated with Firewall Rules: I highly recommend getting familiar with these cmdlets by looking for creative ways to incorporate them into your scripting.
|
get-command *firewall* |

Examples on how to Automate Firewall Rules Across your Enterprise Environment. Click here.

